Computer Repairs Brisbane News - CompuRepair
Thinking About a Laptop Upgrade?
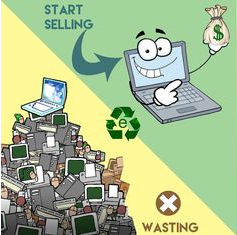
 You want to sell your laptop! Perhaps you’re planning to upgrade to the current model laptops that are available and get rid of your old one. Maybe you have been given a top of the range, fast and powerful laptop for your birthday.
Now you have to decide whether you sell your old one or perhaps present it to a friend or relative.
If it’s quite old you can donate it to a centre that recycles old laptops, but if it still works okay, it would be nice to be able to make a few dollars. If you want to do any of those - sell, give away or donate, there are some things you must do to prepare.
What You have to do Before Selling
Assessment
A realistic assessment of the condition of your laptop needs to be done. Are there any major problems such as a broken or cracked screen? Are all the keys working and are there any missing? Does it charge okay?
When you are selling your laptop, approach it as if you are buying it. Would you buy anything that has problems that need fixing before you can use it? Places like
Computer Repairs Brisbane
are specialists in checking that your laptop is okay or at least recommending repairs.
Fixing the problems or even upgrading the old one can help sell it although the repair costs might be more than the sell price! These are not jobs you can do yourself unless you’re a real handyman with electronics. It makes sense to use the services of an
expert in laptop repairs
to do the work. At least get a quote so you know what you are going to be paying.
You want to sell your laptop! Perhaps you’re planning to upgrade to the current model laptops that are available and get rid of your old one. Maybe you have been given a top of the range, fast and powerful laptop for your birthday.
Now you have to decide whether you sell your old one or perhaps present it to a friend or relative.
If it’s quite old you can donate it to a centre that recycles old laptops, but if it still works okay, it would be nice to be able to make a few dollars. If you want to do any of those - sell, give away or donate, there are some things you must do to prepare.
What You have to do Before Selling
Assessment
A realistic assessment of the condition of your laptop needs to be done. Are there any major problems such as a broken or cracked screen? Are all the keys working and are there any missing? Does it charge okay?
When you are selling your laptop, approach it as if you are buying it. Would you buy anything that has problems that need fixing before you can use it? Places like
Computer Repairs Brisbane
are specialists in checking that your laptop is okay or at least recommending repairs.
Fixing the problems or even upgrading the old one can help sell it although the repair costs might be more than the sell price! These are not jobs you can do yourself unless you’re a real handyman with electronics. It makes sense to use the services of an
expert in laptop repairs
to do the work. At least get a quote so you know what you are going to be paying.
Recycle, Sell, or Donate
If your laptop is way beyond a practical repair job, giving it to a charity or recycling it are good options. There is always someone out there that can find a use for old laptops.
Pre-Sell Preparation of the Laptop
It’s most important that the laptop is cleaned of any personal data (you should have backed it up anyway), and not have missing accessories. These days replacement chargers are easy to buy and instruction manuals can be found online.
When you advertise it, don’t forget to list all the laptop's specifications and to highlight any special software or additional hardware that you may have uploaded over time.
While it should go without saying, the laptop must be have no malware or viruses. You can do that with programs or you can have your favourite
computer specialist like Computer Repair Yarrabilba
make absolutely sure that it’s squeaky clean.
 Demand
The fact that your laptop is old might make it hard to sell. However, a cheap second-hand laptop can be a very useful addition to a young student for research, to a mum at home for her to blog or look up recipes, for an older person to learn how to use a computer. Not everybody needs the latest and the greatest.
Gaming laptops are extremely good sellers. If you had set your laptop up as a gaming device with extra RAM and a good Video card, it will be a lot easier to sell.
Make sure you let your family and friends know that you are looking to sell your laptop. Even though they might not buy it, spreading the sale word of mouth increases the prospective buyer base. If you want to know more what you can do with your old laptop get in contact with
Computer Repairs Logan,
Computer Repairs Yarrabilba,
Computer Repairs Brisbane,
Computer Repairs Ipswich, you can also find us at
Laptop Repairs Springfield Lakes or on the
Gold Coast.
Can't wait then call: 0403-755-519.
Demand
The fact that your laptop is old might make it hard to sell. However, a cheap second-hand laptop can be a very useful addition to a young student for research, to a mum at home for her to blog or look up recipes, for an older person to learn how to use a computer. Not everybody needs the latest and the greatest.
Gaming laptops are extremely good sellers. If you had set your laptop up as a gaming device with extra RAM and a good Video card, it will be a lot easier to sell.
Make sure you let your family and friends know that you are looking to sell your laptop. Even though they might not buy it, spreading the sale word of mouth increases the prospective buyer base. If you want to know more what you can do with your old laptop get in contact with
Computer Repairs Logan,
Computer Repairs Yarrabilba,
Computer Repairs Brisbane,
Computer Repairs Ipswich, you can also find us at
Laptop Repairs Springfield Lakes or on the
Gold Coast.
Can't wait then call: 0403-755-519.
The Benefits of Social Media
By using your own Facebook page, it can help advertise your laptop for sale. These are the times when using social media accounts can be a very good idea. Make sure you list the specs and add a current photo image to the sales page, along with the price.
 EBay, Gumtree or Trade it in
If you have sold stuff either on eBay or Gumtree, then your chances of selling there again are fairly good. You need to adopt all the necessary precautions selling items online.
You can always opt to trade in the laptop. You might not get the price you want but the real advantage is a quick sale and it will probably save you a lot of hassles and frustration of making the sale yourself.
Amazon provide ways and means to trade I the laptop by providing their gift cards or coupons instead of paying in cash. It’s the same with Apple. If your laptop is a MacBook, Apple will offer you a gift card based on the calculated current value of the item.
Last but not least, before you ship your laptop off to the buyer make sure that you have received the money first. Yes, it sounds like common sense, but you would be surprised at the number of people that will send an item to a prospective buyer in good faith.
As you can see there is a lot of preparation work to do when selling a personal computer. Make sure it’s a clean machine! If you have any questions or need help cleaning up your laptop before selling it speak to us at
computer repairs Logan. We are just a call away.
EBay, Gumtree or Trade it in
If you have sold stuff either on eBay or Gumtree, then your chances of selling there again are fairly good. You need to adopt all the necessary precautions selling items online.
You can always opt to trade in the laptop. You might not get the price you want but the real advantage is a quick sale and it will probably save you a lot of hassles and frustration of making the sale yourself.
Amazon provide ways and means to trade I the laptop by providing their gift cards or coupons instead of paying in cash. It’s the same with Apple. If your laptop is a MacBook, Apple will offer you a gift card based on the calculated current value of the item.
Last but not least, before you ship your laptop off to the buyer make sure that you have received the money first. Yes, it sounds like common sense, but you would be surprised at the number of people that will send an item to a prospective buyer in good faith.
As you can see there is a lot of preparation work to do when selling a personal computer. Make sure it’s a clean machine! If you have any questions or need help cleaning up your laptop before selling it speak to us at
computer repairs Logan. We are just a call away.
HDD vs SSD
What Are Their Differences, Which Is Better?
Unless you are a computer repair service person, you might not be aware what an HDD or an
SSD
is if someone suddenly asked you. It's not really difficult to identify what an HDD and an
SSD are. For starters, they have something to do with your desktop or laptop's storage capacity. HDD stands for
hard disk drive and SSD stands for solid-state drive.
In the past, an HDD was only used in desktops or laptops while an SSD was only used in ultraportables. Now,
you can configure all systems to either have an SSD or HDD or both. If you don't know how to do this, you can ask a laptop
repair service company. They offer this kind of service aside from your usual
data recovery Brisbane
needs.
Both the HDD and SSD have the same basic function: they store all your files and applications. They are
also responsible for booting your system. Beyond these similarities, they also have unique characteristics. Below is a
side-by-side comparison between the differences of the HDD and the SSD.
Storage Capacity And Price
SSDs are more expensive than HDDs. For example, an SSD with a 1 Terabyte (1 TB) storage capacity can cost
around $400 while an HDD with the same storage capacity only has a price range of $80 - $180. If you try to break this price
down to per gigabyte, an SSD costs $0.40 per gigabyte while an HDD will cost between $0.08 or $0.18 per gigabyte.
For this reason, most laptops or computers equipped with SSDs will only have between 500GB and 1TB of storage
capacity. You might see an SSD with a maximum storage capacity of 4TB but they are very rare and extremely expensive at this
time.
On the other hand, a 1TB HDD is enough to hold all your files and applications. An HDD also has an almost
infinite read-write capability. Thanks to its magnetic storage method. Your
computer repairs Brisbane
service technician will assure you that an HDD is enough. And you don't have to worry about
running out of storage space.
Moreover, you can also use other storage alternatives, such as an external hard drive or a cloud storage
(link to article) system. As mentioned in our previous posts, additional storage systems are an essential part of protecting
your data against
ransomware
attacks. These separate storage methods will also serve as your data recovery backups.
Speed
Speed with regards to HDD and SSD refers to how fast they read data. An SSD is definitely faster than an HDD.
They boot faster, they transfer your files quicker, and launches and runs your computer apps much faster.
SSDs also do not experience fragmentation. That's because SSDs doesn't have a physical read head. Instead,
it has cells where data can be stored anywhere as well as read and access files at the same time.
However, when the storage disc holds too much data already, the files are written across multiple
sections. In short, they become fragmented.That's when fragmentation happens. Because of this, computers or laptops
equipped with HDD perform slower over time.
On the contrary, HDDs use rotary recording surfaces where files are written sequentially. This method
allows the drive head to read the data in one continuous motion. As long as the files are written this way, then the read/write
times is fast.
But don't go running to your
laptop repairs Yarrabilba
service technician yet. Before you ask him to place an SSD on your computer, there's a catch to its
speed - SSD cells are subject to wear and tear over time.
Want to see the difference between an HDD and SSD drive? Why don't you give an SSD drive a go. CompuRepair will upgrade your computer
or laptop with a latest technology SSD drive of your choice - size and brand. To start the process contact
Computer Repairs Logan,
Computer Repairs Yarrabilba,
Computer Repairs Brisbane,
Computer Repairs Ipswich, you can also find us at
Laptop Repairs Springfield Lakes or on the
Gold Coast.
Call Now: 0403-755-519.
Form And Durability
Another big difference between an HDD and SSD is their form. HDDs are usually around 2.5 or 3.5-inch
in size. Manufacturers are trying to shrink HDDs but they stall as they get smaller.
Since SSDs do not rely on spinning platters like the HDDs, their size has no limitation. Therefore,
they can shrink to a much smaller size. And with laptops becoming much slimmer, SSDs will surely shrink more.
Generally, most computers have an HDD but new ones already have slots for SSDs. In fact, most SSDs
are now compatible with the M.2 slot where you can also install drives even without cables.
In terms of durability, SSDs are far more durable than HDDs. That's because SSDs have no mechanical
parts. So even when you drop your laptop, no tiny sensitive parts can be broken inside.
In contrast, there are tiny mechanical parts inside an HDD. These parts are delicate and sensitive
to movement. If you drop your laptop, there is a possibility that the parts will be broken. You might even lose some
of your data as a result of the fall. At this point, data recovery might be quite a challenge. Don't panic there are
companies like
computer repairs Logan
that can recover nearly any damaged drive.
Choosing Between An HDD And SSD
Both
HDD
and SSD have their advantages and disadvantages. If you ask your local computer
repair services computer repairs Springfield Lakes, they will say that your choice depends on your needs.
If you are looking for speed, then SSD is your choice but they might be too expensive for your
budget. Opting for a cheaper SSD means limited data storage capacity as well. HDD, on the other hand, is cheaper
but they are more sensitive to damage. They also become much slower over time as you store more data.
This might be quite a dilemma but there are some alternatives to solve this. First,
have your laptop repair service check your configuration. Ask them if it is possible to have separate
multiple drives on your computer or laptop.
Another alternative is an
SSHD,
short for solid-state hybrid drive. This is a crossover between an SSD and HDD. It looks
like a full-sized HDD with up to 2TB of storage space. It also has an extra cache of SSD NAND memory.
What an SSHD does is identify the files that you often use. Then, they place these
files in an easily accessible section of the SSD memory. The rest of the files are then placed in the
HDD.
These hybrids might not be as durable as an SSD but they are cheaper. They also give
your speed a much-needed boost.
Another alternative for extra storage is an external hard drive. You can either buy
one or make one using any drive. All you need to do is buy an enclosure and connect it to your desktop or
laptop using a USB. It functions like a normal drive and can be carried anywhere.
In Closing
The computer storage landscape is dynamic. It changes very quickly as new technologies emerge.
Thus, we recommend that you choose a laptop or desktop that has both an SSD and HDD in its system. You can
also choose something that has a hybrid drive in it.
The system might cost you more but you will notice a big difference. You will have longer
lasting storage, speed, and performance every time you turn on and use your computer.
Phishing and You
Phishing
Phishing (pronounced fishing), is it a bad thing? The answer is a resounding yes, and just about everyone is at risk
of losing vital information to phishing including your credit card information, banking information, online account information, and more.
In this brief article you will get a basic explanation of what phishing is, why it is dangerous, and a few tips to help protect yourself.
If you do download malicious software accidentally or opened a phishing email and got infected check out Computer Repairs Brisbane
for more help.
Brisbane,
Logan,
Ipswich,
Springfield Lakes,
Forest Lakes,
North Lakes,
Sunshine Coast,
Yarrabilba or on the
Gold Coast.
Contact Us Now: 0403-755-519.
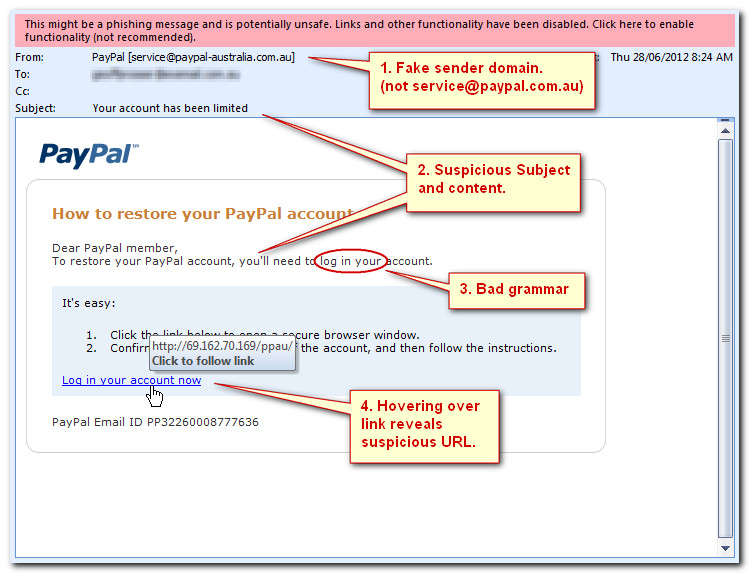
What is Phishing?
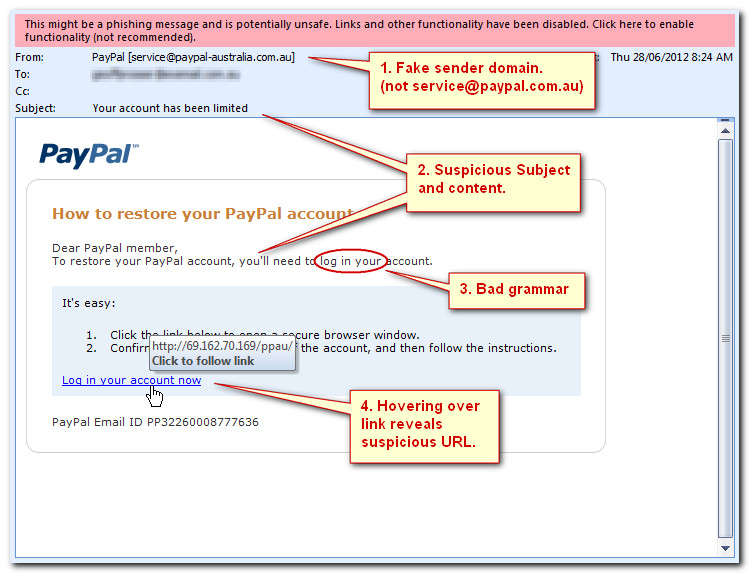
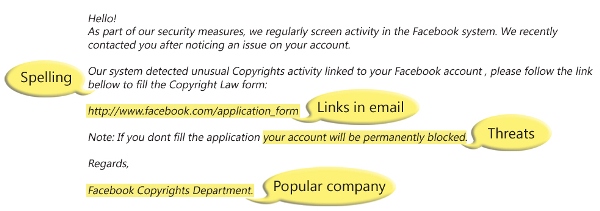
Phishing is an attempt at tricking someone into giving away their private information through electronic communication by
pretending to be from a trustworthy organization. Phishing is a homophone of fishing. This is because both of them use bait to attract and
catch prey. There are many ways phishing can be accomplished, and the use of it has been growing incredibly fast since it first started.
With 12,845 unique phishing reports in January 2005 up to 229,265 unique reports in March of 2016 (according to the
Anti-Phishing Working Group).
Clearly this is not just some small time scam, but something that will most likely affect everyone if it hasn’t already.
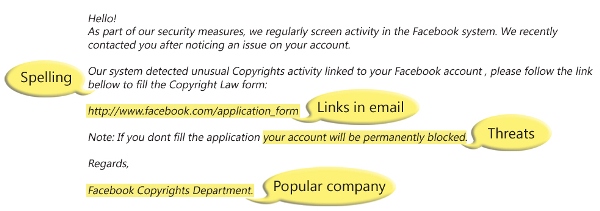
What does a phishing message look like? Often there are spelling or grammar mistakes, which a big company should never
have in their important emails. Threats of loss of service are another red flag to look for. Often times the links in the emails aren’t what
they appear, and lead to various malicious sites. There are many ways to make an email look professional when it isn’t actually. Some of
those ways include an email address that appears to be from the company, a proper signature, and even pictures and font styles of the company
they are imitating. A useful tip is that if you hover your mouse over a link without clicking on it you will see what the actual link you’d
be following is. Most importantly, if you are suspicious of an email you can call the company to verify that they are the ones who actually
sent it. If you’re near Logan, Brisbane or Ipswich and are having an issue, feel free to check out
Laptop Repairs Logan or
Computer Repairs Springfield Lakes
for more help.
Phishing is broken up into four classifications, phishing, spear phishing, clone phishing, and whaling.
Phishing
Phishing involves some kind of online communication that is supposedly coming from a trusted source.
This could be an email, direct message, and more recently, even a text message. The message usually will ask for some kind
of information either sent directly as a response, or by following a link.
Clone Phishing
Clone Phishing is an attack where a legitimate email, that contained an attachment or link, is copied
to create an almost identical email. The big difference is that the attachment or link will be replaced with a malicious
version.
If you need fast and reliable service you can contact CompuRepair at any time. CompuRepair can help with
computer repairs in Brisbane,
computer repairs in Logan,
computer repairs in Ipswich, we also can help with
laptop repairs in Springfield Lakes,
laptop repairs in Forest Lakes,
virus removal North Lakes,
computer repairs on the Sunshine Coast,
computer repairs in Yarrabilba or any IT related issues on the
Gold Coast.
Ring Us Now: 0403-755-519.
Spear Phishing
Spear Phishing is a more effective version of phishing, because it is an attack directed at one person instead
of multiple people. Attackers will usually gather personal information about the target to better personalize their message and
increase the odds of success.
Whaling
Whaling is one of the most lucrative types of phishing scams. These are phishing scams aimed towards high
level executives and upper management of large companies. The messages are generally business oriented. They usually use either
a subpoena or a false company-wide concern to entrap them into giving up their information or downloading malicious software.
The message itself is often not the end of a phishing scam. The link you follow will often look just like the official website,
or at least quite close. There are also some scams that use a more covert method. They’ll use a pop-up window on a site’s
legitimate domain. This can include a pop-up asking for you to login, or asking for you to authorize something. Putting your
information into one of these pop-ups may even download malicious software to your computer and steal your information from the
inside, even if it doesn’t specifically ask for private information.
Conclusion
Phishing does pose a dangerous risk to your online information, but you can protect yourself against it.
Be careful who you give your information to, and watch out for threats from big companies. There are also many ways to report
phishing, including reporting it to the APWG, Scamwatch, CERT, Europol, or even the RCMP. There are a lot of organizations
trying to stop cybercrime like phishing, and they need victims to let them know when these attacks happen. Don’t let yourself
get fooled. Follow the link to
Virus Removal Brisbane if
you’re concerned for your computer’s health.
Computer Upgrade?
Time for a New Computer?
To buy or not to buy, that is the question. Is the computer sitting on your desk good for a few more years, or has
the thing had it? Sure, new computers have appeal: unboxing a clean new machine with the latest, greatest software and booting it up for
the first time, the hassles and flaws of the old clunker fading in the rear view mirror. But before you put down hard-earned money on a
new PC, have a good look at the one you already have. Some simple maintenance or a low-cost upgrade can give it a new lease on life.
Computer repairs Brisbane and
Computer repairs Logan
can help you with the difficult choice to upgrade or replace your computer. Call us for a free consultation.
The Speed Wall
In decades past, new computers had striking speed advantages over old ones; the chips that went into PCs improved
steadily and dramatically. However, for about ten years, new microprocessors no longer offer the big gains they used to. The reasons
are mostly technical, but the latest whiz-bang machines are no longer much faster than last year’s at the same price point. For some
time, chipmakers have been focusing development on sexy Smartphones and not said desktops. So if your five-year-old desktop or laptop
seems slow, a new machine at the same price might not be much better. You can get some improvement by spending double or triple your
initial investment, but even that might not blow your socks off. However, don’t despair; there’s ways to wring more performance from
the PC you already have without breaking the bank.
Memory Upgrade
A RAM (memory) upgrade is one of the easiest and least expensive ways to make your computer faster and more capable.
Modern operating systems such as Windows and Mac OS are designed to take advantage of all memory available; the more you have, the
better it works. Some computers, however, come from the factory with minimal installed memory, keeping the cost low though limiting
the machine’s performance and usability. If you find yourself waiting long stretches whilst your software “thinks”, a memory shortage
may be the culprit. By adding the right memory modules to the computer’s internal slots, its performance can be improved dramatically.
Call us for fast, professional upgrades to RAM and other components! Same-day, onsite computer maintenance and repair in
Brisbane,
Logan,
Ipswich,
Springfield Lakes,
Forest Lakes,
North Lakes,
Sunshine Coast,
Yarrabilba or on the
Gold Coast.
Contact Us Now: 0403-755-519.
Hard Drives
Most modern hard drives have vast storage capabilities compared to older examples from just a few years ago.
Although the average home user might never fill up their computer’s drive space, large media collections, such as photos, video,
and music can use up all the available room on a PC. A space-limited computer can become sluggish or even crash altogether, as
it needs free space for housekeeping and temporary storage. Fortunately, hard drives are easily replaced by a competent technician
and are inexpensive compared to a new PC.
SSDs
A relatively new technology called the Solid State Drive (SSD) replaces traditional mechanical hard drives
with flash memory — a compact, solid-state technology that has been improving by leaps and bounds. Though currently more expensive
than hard drives, SSDs have been increasingly finding their way into consumer PCs. Their main benefit is speed, reducing start-up
times to a few seconds and improving overall performance significantly.
Network setup Brisbane.
We’ll set up a fast, efficient data network for you, or troubleshoot your existing network.
Call us today: 0403-755-519.
Processor Upgrade
Some computers have a special socket inside that lets you remove the old microprocessor and put in a new one. By
simply replacing the chip, you can see a noticeable speed increase. Note however that not many consumer-grade machines have the ability
to replace the CPU chip; it depends on the model.
Malware
Few things in modern life are as frustrating as a malware infection. Viruses can clog your computer with annoying
pop-ups and unwanted adverts, scramble its files, or even shut it down completely. Yes, though you can replace your old computer when
it becomes infested with viruses and malware — and many do —, your money’s better spent on professional cleanup and recovery. With
the right methods, your computer can be restored to its original speedy self.
Slow computer? Don’t junk it — Call us! We do
computer repairs in Springfield Lakes
or any other areas around
Brisbane.
We can remove any unwanted programs including Malware and viruses.
When to Buy
Of course, there are completely sensible reasons for getting a new PC. A very old machine might not be able to run the
latest software, for example. Kids and other family members might need their own computer for school or work. Damage or theft might make
a new machine a necessity. You might want to switch from PC to Mac or the other way around. Or you may have outgrown a budget laptop or
all-in-one that has had limited upgrade options.
Floating in the Cloud
The Cloud — what is it?
You may have read articles mentioning this wondrous, cutting-edge computing technology, or seen an advert for cloud
services, and wondered what the fuss was about. In a nutshell, the Cloud is data storage and other services delivered over the internet.
With traditional computing, the computer is right in front of you; it has fixed limits of data capacity and computing speed. The Cloud, on
the other hand, is a large, flexible “blob” of data resources accessible anytime and from nearly anywhere. The Cloud frees you from the
need to buy and maintain extra computers — the cloud service provider does that for you. Though many cloud services are aimed at business,
some are useful to the average Jane and Joe.
Data recovery Brisbane and
data recovery Gold Coast.
Crashed laptop? Our trained technicians can recover lost files and data from any storage device.
Essential Ingredients
The Cloud delivers internet-based services that can process fairly large amounts of data. To make it work, you need a
recent PC, laptop, or mobile device, an account with a Cloud service provider, and a high-speed internet connection such as cable, Wi-Fi,
or 4G cellular data. A fast connection is essential because you may be moving many gigabytes of data back and forth; older links such as
traditional dial-up would render cloud services too slow to be practical. Virtually all modern devices running current software will work
fine with a cloud service; on the other hand, that old clunker PC you keep in the basement might not, and the simplest cell phones
likewise wouldn’t have enough “brainpower” for the Cloud.
What’s Over There?
Cloud service providers maintain millions of gigabytes of hard drives in large warehouse-like facilities called data
centres or server farms. They use very fast computer networks to manage the torrents of data traffic from millions of customers. The server
farms are housed in secure buildings with controlled access and sophisticated fire prevention. Cloud facilities are also increasingly green,
keeping a careful eye on energy consumption and carbon footprint. In addition, they employ teams of highly-trained technicians to oversee
and maintain thousands of rack-mounted computers, replacing and upgrading them when necessary. Uptime, the measure of computer availability,
is very close to 100 percent; maintenance and other routine tasks are done without affecting customer service.
Laptop repairs Brisbane,
computer repairs Logan,
sick Mac?
Don’t fret! We can help with any computer issue including hardware failure, virus infections or any network issues.
We don't stop just there, we also specialise in Apple Mac hardware and software, and will get you up and running quickly - often the same
day you call us. Ring us to find out what we can do for you: 0403755519.
Example Cloud Services
Many companies provide a variety of cloud services. For example, Apple’s iCloud has data storage, file sharing, and
remote access to your Mac desktop. LiveDrive, Dropbox, and Google Drive offer a convenient way to share large files. Other general cloud
services include word-processing programs, financial management software, and number crunching for business and science.
Network setup Logan.
We’ll set up a fast, efficient data network for you, or troubleshoot your existing network.
Call us today: 0403755519.
Benefits
The Cloud offers several advantages over traditional computing. For example, it is safer from hazards such as flood and
fire; if you have a cloud account and your home or office should suffer these tragedies, your data will still be safe because it is at a
different physical location. The cloud service provider takes responsibility for other risks such as theft, and maintains their own backups.
Their technicians watch over the facilities to ensure the data remains safe. Cloud data is also easily shared across great distances, should
you want to, as it is hosted on the internet. It is easy to upgrade your cloud account for greater speed and capacity should you need it;
unlike a PC upgrade, there’s no downtime involved with a Cloud upgrade.
Cloud Storage
Data storage is one of the simplest examples of a cloud service. You rent a portion of the cloud service’s hard drive
storage, usually many gigabyte’s worth; your computer treats it as if it were an extra hard drive on your desktop. You can use cloud
storage to free up space on your PC’s internal hard drive, to archive important but seldom-used files, to or to share documents with
others.
Cloud Backups
Several companies, including Carbonite, IDrive, Backblaze, and Mozy offer backup services that store data to the Cloud.
With these services, a program on your computer copies files on your hard drive and sends them over the internet to a remote facility. The
program runs on a regular schedule, keeping the backup copies current. If your computer should suffer a data loss, you can recover your
files easily by copying them back from the Cloud. Cloud backup plans cover nearly any situation, from mobile devices and home PCs to
large businesses.
Cloud Apps
You can access many kinds of software services in the Cloud. Application packages such as Google Docs, Microsoft’s
Office Online, and OnlyOffice provide online word processing, spreadsheet, and other common office functions through common web browsers,
taking the place of traditional software installed on your PC. Other business-oriented applications include Salesforce, a customer
relationship management (CRM) system, GoToMeeting, an online conferencing program, and Workday, used for financial and Human Resources
management.
Data backup Springfield Lakes
and
Data backup Ipswich. Backups are
your insurance against serious data loss. We can help you with file transfers and data backups for your home or office, any time.
Call us today — we’ll create a professional backup solution for you.
Ransomeware And Scareware
Latest Threats: Ransomware and Scareware
Viruses. Spyware. They’re enough to give you fits, but they’re now joined by two new gremlins: ransomware and scareware.
Ransomware kidnaps your files and doesn't return them till you pony up some cash. This equal-opportunity offender has recently targeted
thousands of private companies, individuals, hospitals and schools. Another recent addition to the rogue’s gallery, scareware, does far
less damage, posing more of a nuisance than a real threat.
If you have been a victim of a Ramsonware attack, switch off your computer and call the experts at CompuRepair -
Computer repairs Brisbane to minimise the damage
caused by the attack. We will remove the infection and clean up your file system of damaged (encrypted) files and if possible try to
restore / recover encrypted files.
What is Ransomware?
Ransomware comes in two main types: lock screen and encryption. The first blocks you from using your computer; you can’t
run any programs while the lock screen is up. An encryption ransomware hides all your documents — family photos, music, and any other
personal data — with a secret code, then erases the originals. The program displays a message telling you your data is gone, and if you want
to access it again, you must send money to an account. When the criminals receive the money, they send you the code; when you type it in to
the ransom message on your screen, the software releases your computer or your files.
What is Encryption?
Encryption is a process in your computer that encodes information, scrambling it and making it unreadable to anyone not
in possession of a special mathematical key. Most online retailers and banks use encryption protect data on the internet because it guarantees
the privacy and security of your transactions — an eavesdropper looking for juicy information would receive only gibberish. Encryption is
also used to convert documents and data files into a secret, private form readable only to those who know the password. Ransomware uses
encryption to lock and hide your own files from you, unlocking them only when the software is given the correct code.
How do Ransomware Attacks Happen?
Ransomware is not a normal part of Windows, macOS or other standard operating systems; it always comes from outside
your computer. Typically, ransomware must get installed on your computer, by clicking an attachment link in an email, or by downloading
software from an infected source. Ransomware is usually hidden in other content, revealing itself later only when it’s done its dirty
work.
Laptop repairs Logan.
Has your Laptop's data been destroyed by a Ransomware attack? Get in contact with us, we will help you to recover as much of your data
as possible.
A Typical Message
Ransomware messages vary, but all display an impossible-to-ignore screen in bright colours informing you that your files
are unavailable and telling you to send money. A typical message follows:
Your personal files are encrypted by CTB-Locker. Your documents, photos, databases and other important files have
been encrypted with the strongest encryption and unique key, generated for this computer.
You have only 96 hours to submit the payment. If you do not send money within provided time, all your files will
be permanently crypted and no one will be able to recover them.
Warning! Do not try to get rid of the program yourself. Any action will result in decryption key being destroyed.
You will lose your files forever. Only way to keep your files is to follow the instruction.
Fixing a Ransomware Attack
The best way to foil ransomware is not to get it in the first place. Avoid sketchy websites and don’t click on links
embedded in emails, even if they appear to come from someone you know. Adult and software-pirate websites in particular have a reputation
for being hotbeds of malware. If your computer has been infected, call Compurepair -
Computer repairs Springfield Lakes for
expert assistance in recovering your files.
Is your computer running slow? Is your laptop not booting up? Call
Laptop repairs Brisbane.
We are here 24/7 to help with your IT needs. No problem is to small or to big and we come out the same day you call and fix any issue you
experience. Call now: 0403755519.
Ransomware Payment
A relatively new type of digital currency, called Bitcoin, has been favoured by data kidnappers for payment.
Bitcoin is not part of the standard banking system and bypasses the normal ways of tracing money, making ransomware thieves harder to
catch.
Backups
In many cases, you can recover from a ransomware attack by reformatting your hard drive, reinstalling Windows or
other operating system software, then copying your files from your most recent backup. What’s that you say — you don’t have any backups?
If you’ve been waiting for the right time to begin this essential practice, let ransomware be the excuse you’re looking for. This is
especially important to small business owners, whose livelihoods depend on the information in their PCs and mobile devices.
Variants
Ransomware is not a single program but a host of programs that have evolved rapidly in recent years. Examples include
Alfa Ransomware, ZeroLocker, CTB-Locker, CTB-Faker, Crypt0L0cker and CryptXXX.
“White Knight” Utilities
Some computer security companies, including Kaspersky Labs, Trend Micro, and Cisco offer utilities that remove the
offending programs and recover your files without your having to pay a ransom.
A Bad New Twist
Ranscam, a program that recently surfaced, has taken the ransom game to a whole new low. Like other ransomware, it
displays a message demanding money. However, Ranscam simply deletes your files; it does not encrypt or otherwise save them. It also
alters parts of Windows, preventing recovery of deleted files that would otherwise be possible. When the hapless victim pays the ransom,
the files are still lost.
Network setup Springfield Lakes
and
Network setup Logan. You have issues
connection to the internet? Your computers can't talk to each other? Printer disappeared from your Local Area Network (LAN)? CompuRepair
can help to repair any network errors or help you to setup your LAN. Call for a quote: 0403755519.
What is Scareware?
When you visit a website infected with scareware, you will get a pop-up message intended to scare you, such as “Your
account has been turned over to the police,” or “Your computer has a virus.” In reality, however, the software merely hijacks your
browser temporarily. You might not be able to close the tab or the browser window. Scareware does nothing more than scare you into
thinking your computer has been compromised, and you have to take some action, but it’s not true.
Dealing with Scareware
First of all, don’t panic. The scareware programming makes it hard to close the offending tab or window, but you can
usually resolve the situation by quitting the browser program. In some instances, you must stop the browser by issuing a “kill” command,
which varies by operating system. Avoid revisiting the web site that carried the scareware message. If the message is trying to sell
you something, such as an anti-virus program, treat it as a scam and ignore the pitch.
Ransomware and Scareware: How to Tell the Difference
Usually, scareware takes place entirely within the web browser; in a tab or pop-up window. Ransomware, on the other hand,
is an independent program which may prevent you from using other programs on your PC. Ransomware changes files and data on your computer,
but scareware leaves no lasting effect.
Unveiling the Mystery: Why Is My Computer Slow?
Keeping Your Cool: Troubleshooting Computer Overheating Issues
Restoring Brilliance: Expert Solutions for Microsoft Surface Laptop Repairs
The Hidden Peril: Understanding the Impact of Water Damage on Your Laptop
Navigating the Crossroads: Upgrade, Repair, or Replace - CompuRepair's Guide for Smart Computer and Laptop Decisions
Decoding the Apple Orchard: A Guide to Choosing the Right Mac - CompuRepairs's Expert Advice
CompuRepair Guide: Seamless Email Client and Email Account Setup
CompuRepair Insight: Unveiling the Pine Gap Facility in Alice Springs
CompuRepair's Guide: When to Consider Upgrading to Windows 11
CompuRepair Tech Update: Intel Unveils 14th Gen Core Desktop Processors for Enthusiasts
CompuRepair Insights: When to Install or Upgrade Your Operating System
CompuRepair Explains: What is 3D-Printing and How to Setup Your 3D Printer
Maximizing Profits with Crypto GPU Mining and Chia Farming: A Comprehensive Guide by CompuRepair
Creating the Perfect Home Office: Tips, Tricks, Setup and Maintenance Guide
Decoding the Blue Screen of Death
Here at CompuRepair, each and every one of our computer technicians has been carefully selected; we make sure that they
have the appropriate technical expertise and experience. So, if you need same day, onsite
computer repairs Brisbane,
Logan, Ipswich, Springfield Lakes, Forest Lakes, North Lakes, Sunshine Coast, Yarrabilba
or on the
Gold Coast
then
Contact Us
Now: 0403-755-519.
More Posts about Computer Repairs
Welcome to CompuRepair, your trusted computer repair service provider. We understand how frustrating it can be when your computer or laptop encounters issues, disrupts your work, or hampers your productivity. That's why we are here to provide reliable and efficient solutions to all your computer-related problems. We offer same day service, are responding fast to any call outs and offer reliable service.
At CompuRepair, we have a team of highly skilled and experienced technicians who are passionate about computers and technology. Whether it's a hardware malfunction, software glitch, virus infection, or network connectivity problem, we have the expertise to diagnose and resolve the issue promptly.
Our range of computer repair services includes:
Hardware Repairs:
Repairing computer hardware issues requires a certain level of technical expertise and caution. While I can provide you with some general guidance, please note that hardware repair can be complex, and it's often necessary to seek professional assistance if you're unsure or uncomfortable with the process. CompuRepair uses high-quality replacement parts to ensure optimal performance and reliability.
Here are some steps to consider when attempting to repair computer hardware issues:
Identify the problem:
Determine the specific hardware component that is causing the issue. This could be the motherboard, CPU, RAM, hard drive, graphics card, power supply, or other peripherals.
Gather information:
CompuRepair will research the symptoms you're experiencing online to understand common causes and potential solutions. We will access user forums, support websites, or official documentation related to your hardware or specific issue.
Safety precautions:
Before working on any computer hardware, it is important to turn off the computer and unplug it from the power source. Ground yourself by touching a metal surface or wearing an anti-static wristband to prevent static electricity from damaging sensitive components.
Diagnostic tests:
We run diagnostic tests to pinpoint the faulty component. Software tools like memtest86+ can help identify faulty RAM, while hard drive diagnostic tools like CrystalDiskInfo can check the health of your storage device. Your computer's BIOS may also have built-in diagnostic tools. Sometimes it is necessary to take the computer off-site to test your hardware as it can be time consuming to do this on-site.
Basic troubleshooting:
Of course, we will start with the simplest solutions. Check all cable connections to ensure they are securely plugged in. Clean dust and debris from the components and vents. Restart the computer and see if the issue persists.
Component replacement:
If you have identified a faulty hardware component, you may need to replace it. This process varies depending on the component. For example:
RAM:
Remove and reseat the RAM modules, ensuring they are properly aligned and firmly seated in their slots.
Hard drive:
Replace the faulty drive by disconnecting cables and unscrewing it from the case, then install a new drive and reconnect the cables.
Graphics card:
Remove the old card by unscrewing it from the case and disconnecting any power connectors, then install the new card and reconnect all necessary cables.
Seeking professional help:
If you're uncomfortable or unsure about handling hardware repairs, it's best to consult a professional technician or take your computer to a certified repair center. We at CompuRepair have the necessary tools, expertise, and experience to diagnose and fix hardware issues safely.
Remember, computer hardware repair can be challenging, and it's important to exercise caution to avoid causing further damage. If you're unsure about any step or encounter unexpected difficulties, it's best to seek professional assistance. We at CompuRepair can help you with this, give us a ring.
Software Troubleshooting:
Our technicians are well-versed in identifying and resolving software-related issues. Whether you're experiencing operating system errors, software crashes, compatibility issues, or other software-related issues, CompuRepair's team of experts can help identify and fix the problem.
To troubleshoot software issues, CompuRepair may employ various techniques such as:
Remote Assistance:
With your permission, CompuRepair can remotely access your computer to diagnose and fix software problems. They can navigate through your system, identify the root cause of the issue, and apply appropriate solutions.
Software Analysis:
CompuRepair's technicians have extensive knowledge and experience with different software applications and operating systems. They can analyze error logs, system configurations, and software settings to pinpoint the source of the problem.
System Updates and Patches:
Outdated software can lead to compatibility issues and vulnerabilities. CompuRepair can ensure that your software is up to date by installing the latest updates and patches provided by software vendors.
Software Reinstallation or Repair:
If a particular software application is causing issues, CompuRepair can perform a reinstallation or repair process. This involves uninstalling the problematic software, removing any associated files, and then reinstalling it to ensure a fresh installation without any conflicts.
Malware and Virus Removal:
Sometimes, software issues can be caused by malware or viruses. CompuRepair can perform thorough malware scans and remove any malicious software that may be affecting your system's performance.
Configuration and Optimization:
CompuRepair can review your software configurations and optimize settings to ensure smooth operation and prevent conflicts between different software applications.
It's important to note that while CompuRepair can help troubleshoot software issues, they may have limitations based on the specific problem or complexity of the situation. In some cases, it may be necessary to consult with the software vendor or seek specialized support for certain applications.
Virus and Malware Removal:
If your computer is infected with viruses, malware, or spyware, we have the tools and expertise to eliminate these threats and restore your system's security.
Data Recovery:
Accidentally deleted important files? Don't worry. We offer data recovery services to retrieve lost data from hard drives, SSDs, USB drives, and other storage devices.
Network Setup and Troubleshooting:
We can assist you in setting up and configuring your home or office network. Whether it's Wi-Fi connectivity issues, network speed problems, or router configuration, our technicians can provide reliable solutions.
Upgrades and Optimization:
If your computer is running slow or needs an upgrade, we can help. We offer hardware and software upgrades to enhance your system's performance, including RAM upgrades, SSD installations, and operating system optimization.
Custom-Built Computers:
Looking for a personalized computer built to your specifications? We can design and assemble a custom-built computer tailored to your needs, whether it's for gaming, graphic design, or professional applications.
At CompuRepair, we prioritize customer satisfaction and aim to provide excellent service at competitive prices. Our technicians are friendly, professional, and committed to delivering timely and reliable repairs.
Contact us today to schedule an appointment or inquire about our services. Trust CompuRepair for all your computer repair needs, and let us bring your devices back to life!
 You want to sell your laptop! Perhaps you’re planning to upgrade to the current model laptops that are available and get rid of your old one. Maybe you have been given a top of the range, fast and powerful laptop for your birthday.
You want to sell your laptop! Perhaps you’re planning to upgrade to the current model laptops that are available and get rid of your old one. Maybe you have been given a top of the range, fast and powerful laptop for your birthday. 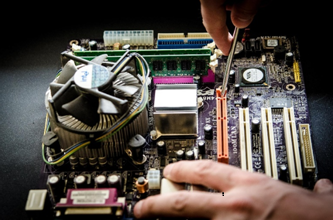 Demand
Demand EBay, Gumtree or Trade it in
EBay, Gumtree or Trade it in